What Is Payment Tokenization? How It Works and Why It Matters
- 10 min read
Payment tokenization is the process of turning sensitive credit card data into a unique identifier known as a token that has no meaning on its own.
It keeps payment data out of fraudsters’ hands and gives customers more convenient payment experiences by powering technology like mobile and e-wallets.
B2B ecommerce is booming, set to reach $1.7 trillion in 2022, a 12% jump from last year.
This is exciting news for merchants, but it brings new challenges. Online sales come with elevated risk and a need for reinforced security. Yet in their haste to adopt online sales channels during the pandemic, B2B companies may not have fully understood the security implications of doing so.
Accepting digital payments requires having a strategy and technology in place to keep sensitive customer data secure. Payment tokenization technology is one important way B2B merchants can transact online while protecting cardholders and themselves.
In this blog, we’ll explain how payment tokenization works (with an example to help put things into context) and why it matters for merchants.
What is payment tokenization?
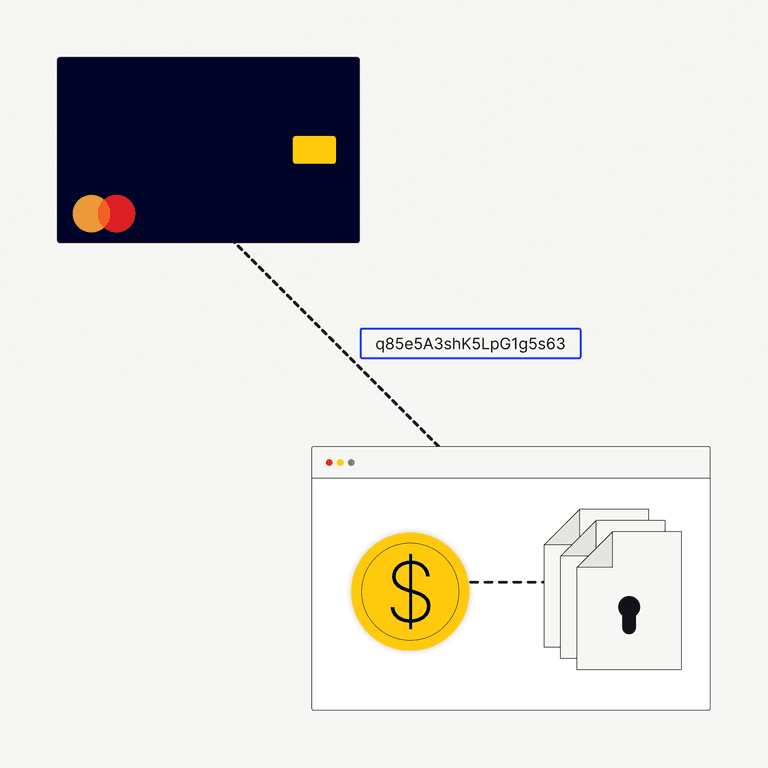
Tokenization is the process of turning sensitive data into a unique identifier known as a token, which has no meaning on its own. In the case of online sales, the unique token—often a string of random characters—is linked to your customer’s credit card number but can’t be deciphered by hackers.
Tokenization allows you to avoid handling and storing customers’ sensitive data, reducing risk, and helping you remain compliant with data-handling standards. Tokenized payments also make it easier for customers to make purchases across multiple channels such as ecommerce, point of sale, and accounts receivable using the same payment method.
Payment tokenization is also the technology that makes virtual cards possible, which is where buyers can make secure digital purchases using an automatically generated 16-digit number that’s only good for a limited number of transactions.
How does tokenization work?
Your customer’s payment—whether made online or in-person through a POS system—sets off an automated process whereby the payment processor (via the payment gateway) substitutes your customer’s credit card information with a unique randomized token to complete the transaction. In many cases, the token is the same length and format as the credit card number, allowing it to integrate seamlessly into your existing payment acceptance systems.
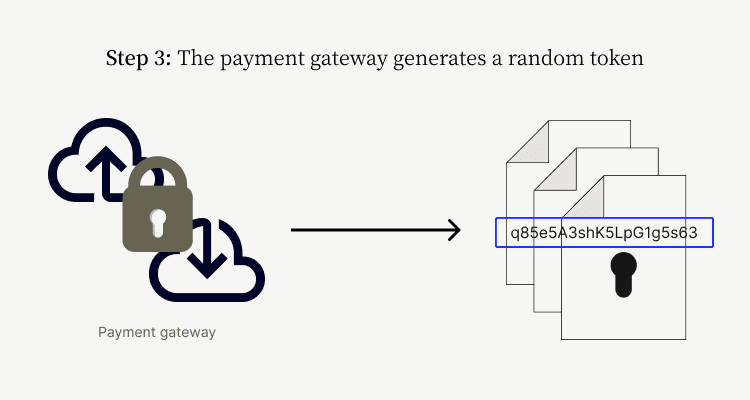
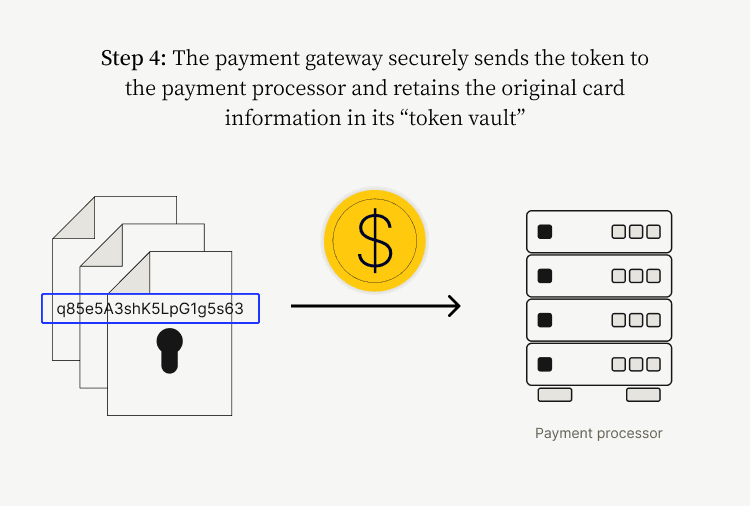
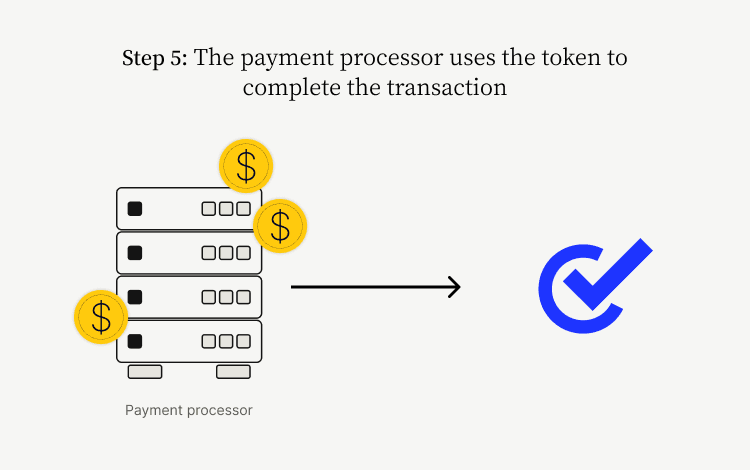
Here’s what the whole payment tokenization process looks like:
- Step 1: Your customer makes an order online using their credit card
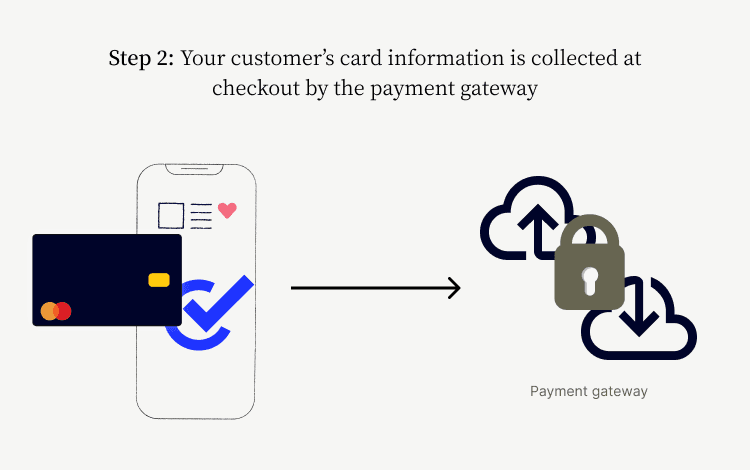
- Step 2: Your customer’s card information is collected at checkout by the payment gateway
- Step 3: The payment gateway generates a random token
- Step 4: The payment gateway securely sends the token to the payment processor and retains the original card information in its “token vault”
- Step 5: The payment processor uses the token to complete the transaction
Do multi-use tokens exist?
Tokens can be single-use or multi-use—referred to as non-persistent and persistent, respectively. With a persistent token, a repeat customer’s data is identified by the same token each time they order. This makes future transactions easier for customers, while at the same time, the original card data never touches your systems.
What is the difference between payment tokenization and encryption?
Tokenization and encryption have the same function: keeping sensitive data safe using cryptographic technology. However, they serve this function in differing ways.
While encryption relies on a mathematical formula that can be decoded into the original data, payment tokenization uses a non-mathematical (read: random) approach that cannot be reversed into the original data except under rare, highly controlled circumstances.
An example of payment tokenization in action
Let’s look at a fictitious example of how payment tokenization works. Imagine that Tony’s Taco Emporium—a multinational restaurant chain—is a repeat customer of the Best Box Company, a global distribution company that makes the most durable take-out food containers around.
When Tony’s Tacos first placed an order on Best Box’s website using their corporate credit card, the payment gateway generated a random token masking their primary account number (PAN).
Because Tony’s Tacos is a regular customer, Best Box’s gateway will reuse that same token every time they order food containers. Best Box can see Tony’s Tacos’ purchase record and recall that same payment information without having to physically store the company’s credit card number.
When Tony’s Tacos orders from their other suppliers online, however, an entirely new token will be created.
PCI Data Security Standards and Tokenization
The Payment Card Industry Security Standards Council (PCI SSC), a global forum comprised of payments industry stakeholders, has established rules called the PCI Data Security Standards (PCI DSS) that businesses must follow to protect cardholder information. These standards define how merchants should obtain, handle, and store credit card data, and how they should monitor security controls.
The PCI DSS, which the PCI SSC updates every three years, includes four levels of compliance, which are defined by factors such as a merchant’s volume of credit card transactions and its data security record. While PCI DSS compliance is not federal law in the US, any payment processor you work with should be in compliance with these rules.
How does credit card tokenization reduce “PCI scope”?
Credit card tokenization is a central component of compliance with PCI DSS. This is because tokenization reduces a company’s “PCI scope,” which is how the industry refers to all the people, processes, and technologies that store, process, or transmit credit card information.
It covers all the elements of a business that interact with cardholder data or could affect its security, otherwise known as the cardholder data environment (CDE). Any element of the business that is part of the CDE is also part of the PCI scope and is referred to as “in scope.”
Reducing the size of your CDE limits your PCI scope and shrinks the number of vulnerabilities in your payment process. It’s a good idea for every business to limit its PCI scope as much as possible, as the greater number of business elements you have in scope, the more challenging it is to secure your CDE from breaches by bad actors.
4 benefits of payment tokenization
Beyond assisting your ability to stay in PCI compliance, payment tokenization has numerous benefits for your business, including:
1. Better customer experience
Tokenization is the technology that makes secure online ordering, virtual cards, mobile wallets, and recurring payments possible. Customers like the convenience of using these features and tend to make more purchases when there are as few steps in the transaction experience as possible.
Research shows that 97% of customers have abandoned an online transaction because the process was too complex. When customers’ experience of making payments to you is exceptionally convenient, they’ll have a more positive association with your brand.
2. Increased customer loyalty
Customers are extremely concerned about the safety of their sensitive data and are much more likely to stick with your company if they have confidence in your security methods.
Surveys show that 78% of consumers would stop doing digital transactions with a brand if that company experienced a breach. A further 49% said they would not register with any online service that had recently experienced a breach. Tokenized payments offer the most secure environment possible for your customers’ transactions.
3. Reduced risk of data breaches
Payment tokenization is also associated with a lower risk of data breaches. In fact, Verizon reports in their Payment Security Report that between 2014 and 2019, it never saw a data breach occur in a company that was up to date with their PCI compliance. What’s more, 53% of companies were confirmed to be non-compliant at the time they experienced a breach.
Data breaches can be very costly and often require companies to pay heavy fines and fees. Additionally, businesses that are associated with data breaches can lose customer trust.
4. Less fraud and fewer chargebacks
Because a payment token can’t be traced back to cardholder information, if bad actors did somehow get a hold of the tokenized data, there’s not much they’d be able to do with it. This results in a reduced risk of payment fraud and lower instances of chargebacks (which is where customers dispute charges directly with their bank).
Companies whose transactions are associated with chargebacks bear some costs—usually a fee of around $20-100 per instance, as well as high penalties for a persistently high volume of chargebacks. Payment tokenization is an important tactic for avoiding these costs.
Partnering with the right payment processor
Not all payment processors are created equal when it comes to data handling and security. When deciding which payment processor to work with, look for one that does all of the following:
- Tokenizes payment data across all sales channels, including ecommerce, point of sale, and accounts receivable
- Securely stores data outside of PCI scope to limit your interactions with sensitive data
- Integrates with your ERP for greater security and lower processing fees
- Supplements tokenization with other fraud-mitigating tactics like card verification value (CVV) matching and address verification
As Versapay’s VP of Payments Chris Adams says, “It's important that all businesses accepting digital payments deploy a fraud mitigation strategy. It should include automated tools to verify the identity of a customer and provide real-time fraud scoring to properly evaluate the risk of a transaction.”
Versapay does all of the things on the above list, acting as your trusted partner to ensure top-notch security as you accept payments electronically.
Download our ebook,Payment Fraud Explained, to learn more about payment security threats and how Versapay can help protect your business.
About the author

Katie Gustafson
Katherine Gustafson is a full-time freelance writer specializing in creating content related to tech, finance, business, environment, and other topics for companies and nonprofits such as Visa, PayPal, Intuit, World Wildlife Fund, and Khan Academy. Her work has appeared in Slate, HuffPo, TechCrunch, and other outlets, and she is the author of a book about innovation in sustainable food. She is also founder of White Paper Works, a firm dedicated to crafting high-quality, long-from content. Find her online and on LinkedIn.


